1.Objectives
1.The Data Protection Act 2018 controls how personal information is used by corporations or public bodies. Its rules require everyone who collects data to follow strict rules, and to keep information safe.
2.The objective of this KCN policy is to ensure that KCN obtains, stores, uses, and discloses of such information in line with legislation, no matter how such information is held.
3.The policy applies where an individual requests a copy of their own personal data, or where a third party, parent or legal guardian acts on their behalf with their permission or under a legal authorisation.
2.Personal data
1.Personal data is information that relates to a living individual who can be either:
Identified from that data; or can be identified from the information combined with any other information that is in the possession of the person or organisation holding the information.
2.Basic personal data includes name, address, date of birth, telephone numbers and bank account details. It may also include recorded opinions about an individual which will form part of the personal data disclosable to them.
3.The Data Protection Act also identifies “sensitive personal data”. Such data includes racial or ethnic origin, physical or mental health conditions, offences or alleged offences, religious beliefs and sexual life. Explicit consent is required from the individual for the collection and processing of such data.
4.Procedures for consent are in place.
3.Principles of good practice
Article 5 of the GDPR sets out seven key principles which lie at the heart of the general data protection regime.
Article 5(1) requires that personal data shall be:
(a) processed lawfully, fairly and in a transparent manner in relation to individuals (‘lawfulness, fairness and transparency’);
(b) collected for specified, explicit and legitimate purposes and not further processed in a manner that is incompatible with those purposes; further processing for archiving purposes in the public interest, scientific or historical research purposes or statistical purposes shall not be considered to be incompatible with the initial purposes (‘purpose limitation’);
(c) adequate, relevant and limited to what is necessary in relation to the purposes for which they are processed (‘data minimisation’);
(d) accurate and, where necessary, kept up to date; every reasonable step must be taken to ensure that personal data that are inaccurate, having regard to the purposes for which they are processed, are erased or rectified without delay (‘accuracy’);
(e) kept in a form which permits identification of data subjects for no longer than is necessary for the purposes for which the personal data are processed; personal data may be stored for longer periods insofar as the personal data will be processed solely for archiving purposes in the public interest, scientific or historical research purposes or statistical purposes subject to implementation of the appropriate technical and organisational measures required by the GDPR in order to safeguard the rights and freedoms of individuals (‘storage limitation’);
(f) processed in a manner that ensures appropriate security of the personal data, including protection against unauthorised or unlawful processing and against accidental loss, destruction or damage, using appropriate technical or organisational measures (‘integrity and confidentiality’).”
Article 5(2) adds that:
“The controller shall be responsible for, and be able to demonstrate compliance with, paragraph 1 (‘accountability’).”
•processed fairly and lawfully
•obtained and processed for a specific purpose
•adequate, relevant and not excessive
•accurate and up to date
•held for no longer than necessary
•processed in accordance with the rights of the data subjects
•kept secure from unauthorised processing or disclosure
•not transferred outside the EEC area unless the same safeguards apply
1.KCN will also seek to comply with the Caldicott Principles that govern the use and management of personal information that allows an individual to be identified. These are :
•be able to justify the purpose of how they use and manage that information
•not use such information unless it is necessary
•use the minimum necessary amount of information
•ensure it is accessed on a strictly need-to-know basis
•ensure those accessing it are aware of their responsibilities
•understand and comply with the law
•be aware that sharing information is as important as maintaining confidentiality
2.KCN is renewing its membership of PQASSO – Practical Quality Assurance System for Small Organisations (now Trusted Charity), and seeks to meet its performance standards.
3.Kingston Carers’ Network
1.KCN representatives
1.1.Trustees should satisfy themselves that the CEO has effective systems and procedures in place as outlined in this policy, and other policies and protocols relating to Information Governance.
1.2.Staff and volunteers must follow the guidelines in these policies and in their Handbooks when collecting, maintaining, storing and disclosing of personal information. Failure to adhere to the Data Protection Act 2018 may lead to disciplinary procedures.
2.Data Protection Officer
2.1.KCN will appoint a data protection officer to carry out its responsibilities under this policy. The officer must maintain a record of all information requests as detailed in the sections detailed below, and follow the prescribed procedures.
2.2.The officer will annually lodge a statement with the Information Commissioner describing the purposes for which KCN process personal information. The details are available from the Commissioner’s office at:
Wycliffe House, Water Lane, Wilmslow, Cheshire, SK9 5AF
01625 545 745ico.org.uk
Name of Data Protection Officer Kate Dudley
RoleChief Executive
3.KCN Responsibilities
3.1 Ensure that all personal and sensitive organisational information, however received, is treated as confidential with regard to the terms of the Data Protection Act 2018 and the Human Rights Act 2018. This includes:
•Anything of a personal nature that is not a matter of public record about a carer, the cared for person, job applicant, member of staff, volunteer or trustee.
•Sensitive organisational information.
3.2 Comply with the law in obtaining, processing and using personal information and in the protection and disclosure of that information, as defined in the Data Protection Act 2018. Comply with the Data Protection Act 2018 in relation to the rights of access to the data of data subjects.
3.3 Ensure that sensitive personal information will not be disclosed to a third party without the prior, informed consent of the individual including family members concerned other than in exceptional circumstances. These include:
•To comply with the law or a court order.
•Where there is a clear health or safety risk (or evidence of fraud)
•Anonymously, for statistical research purposes.
3.4 Not gain or seek to gain access to information other than that for which KCN has authority. In general:
•Staff and volunteers will have access to the information they need to know to carry out their work and have a duty to respect the confidentiality of that information.
•The purpose, and the people likely to have access to sensitive personal information, will, where possible, be explained and informed consent obtained, before such information is recorded.
•References to carers and/or the cared for person in meetings and reports will, normally, be anonymous, although sharing of such information may be necessary at internal meetings.
5.Recording and Disposal of Personal Information
1.This Procedure relates to all records of personal information including paper documents, computer records, photos and other images. Individuals have the right to see all such information.
2.If an individual objects to the records held or to actions taken as a result of these records, they have the right to take KCN to court under the Act.
3.Certain types of personal information are classified as ‘sensitive’ and KCN needs the individual’s explicit permission to hold this data.
4.When making entries in the Carer Controls database and for inclusion in paper files, the entry must conform to the following criteria: relevant and brief; factual and accurate; sustainable in court.
5.KCN should not keep personal data for longer than is necessary to fulfil the purposes for which it is held.
6.Data Security
1.The Act requires that personal information is recorded accurately, confidentially, and securely. Measures should be taken to prevent unauthorised or unlawful processing of personal data and against accidental loss or destruction. Attached are Guidelines that set out steps to be taken by staff and volunteers to fulfil their obligations under the Act. Reference should also be made to the KCN Electronic Communications Policy.
2.An information breach is any event which results, or could result, in the disclosure of confidential information, or put the integrity or operation of any data system at risk. Such a breach should immediately be reported to the CEO. The CEO should: investigate the reason for the breach: assess the likely impact; notify where felt necessary the individual, the police and the Information Commissioner; and formulate a recovery plan.
7.Requests from Carers for Information
1.Requests for Information:
A request will only be accepted either in writing or by e-mail and will be passed to the Data Protection Officer (CEO) who, in consultation with the Office Manager will action the request. It must be recorded in a log of Data Protection Information Requests and is subject to an administrative fee of £10, payable by the person requesting the information.
2.Providing Information:
1.Information may be in paper or computer form (both are covered by the 2018 Act) and must be provided within 40 days of the receipt of the administration fee (not the request). A copy of all information provided will be kept with the log.
2.A description will be given of the personal data held, the purpose for which it is being processed and those to whom the data is or may be disclosed. A copy of the actual personal data held will be given whenever possible (e.g. extracts from the database).
3.The source of personal data held will be supplied with the exception of information which will identify third parties unless their permission has been obtained, as per the attached guide. KCN will ensure that all relevant information is located and provided.
3.Procedure – the Data Officer will :
1.Maintain a log of all information requests and will record receipt of the request and fee and all subsequent actions.
2.Acknowledge receipt of the request in writing and give the date by which the information will be provided.
3.Contact relevant staff within KCN in order to collect the required information which may be obtained from any or all of KCN’s data systems.
4.Collate the information provided and forward it to the individual making the request. An accompanying letter will state that a personal meeting can be arranged if further detail/explanation of the data is required.
5.Arrange a personal meeting on receipt of a request in writing or by e-mail. The meeting will be attended by all relevant personnel including the Data Protection Officer.
6.Keep a copy of all information provided and take minutes at any personal meeting. This information will be retained with the log in case of subsequent court action.
4.Amending Personal Data:
1.Requests for amendment or correction of the personal data held, should be in writing. Where appropriate, the Data Protection Officer may request evidence in support of the amendment or correction. In deciding whether an amendment or correction should be made, the Data Protection Officer will liaise with the relevant staff members.
2.Where an amendment or correction is refused, a letter explaining the reasons for refusal is sent. A note of the request and reasons for refusal is appended to the file.
8.Requests from Third Parties for Information
1.Requests for Information:
In general information can only be given out with the consent of the individual.
Where a third party makes a request it must be either :
•under written authorisation from the individual to act on their behalf
•or under proof of being lawfully appointed (e.g. Power of Attorney or Protection Order)
•or being made by a parent or legal guardian acting for a child
•a request relating to the prevention of crime or the apprehension or prosecution of offenders
2.Providing Information:
2.1The Data Protection Officer should log the request. The person or organisation seeking the information should be informed that consent will be obtained from the data subject before the information is disclosed.
2.2The DPO should write to the person concerned and ask for their written consent, explaining the nature of the information sought, and if consent received, disclose the information requested.
2.3The exception to this is where information is requested for the purposes of the prevention or detection of crime or the apprehension or prosecution of offenders. The request must be in writing and must clearly state the reason for the request and the implications of KCN’s failure to disclose.
9.Sharing Data
1.Personal Identifiable Data (PID) is information about an individual that will single them out. Such data should only be shared with another organisation for a specific lawful purpose or where appropriate consent has been obtained. For consent to be legally valid the individual must: be informed; have the capacity to issue the consent; and give the consent voluntarily.
2.Sharing of such information with a partner organisation should be incorporated into an Information Sharing Agreement which describes the specific purposes and terms under which that data is processed. As we are a relatively small organisation, KCN should be prepared to accept an Agreement drawn up by the particular partner.
3.When personal data is used for purposes other than its primary use, it should be de-identified (anonymised) so that it is impossible to single out an individual.
4.Under the Freedom of Information Act 2000 anyone has a general right of access to all types of recorded information held by public bodies. Requests under this Act should be referred to the CEO.
10.Other linked KCN documents
The KCN Board of Trustees acknowledges that it needs to review its protocols, policies and guidelines relating to Information Governance. This policy update covers a substantial section of its responsibilities, along with other documents listed below.
Safeguarding Vulnerable Adults Policy
Child Protection Policy
Client Confidentiality Policy
Electronic Communications Policy
Staff and Volunteer Handbooks
New documents
Archiving, Security and Disposal of Records
Data Breach Procedures
The attached appendices form part of this policy:
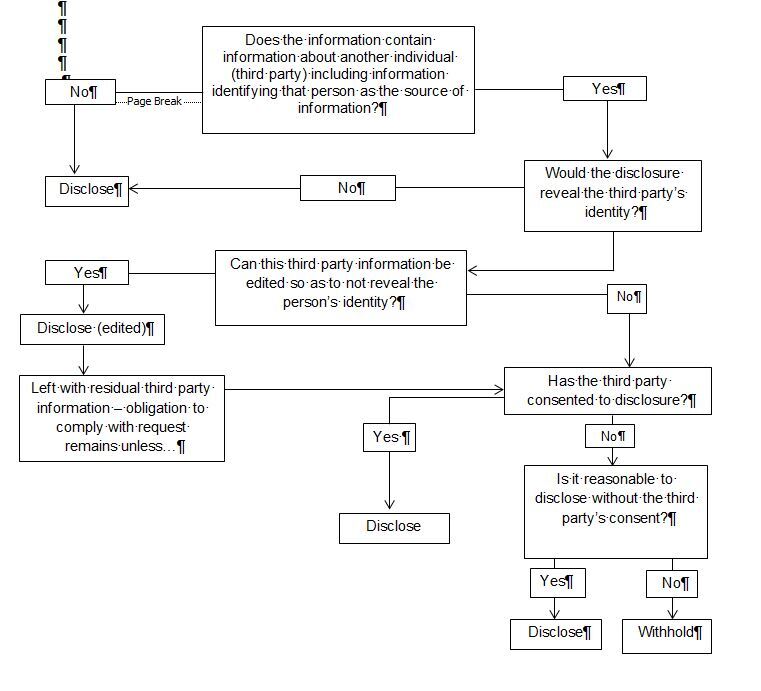
(1)Disclosure Guideline Flowchart
(2)Keeping Information Secure – Guidance
(3)Data Breach Protocols
(4)Privacy Statement
(5)Parental/Young Carers Consent Form
The attached “Keeping Information Secure” should become part of the Handbooks.
Review date : to comply with Information Governance review.
Appendix 1
Disclosure Guideline Flowchart - Guide to Information that may identify a Third Party
When preparing information for disclosure the Data Protection Officer should consider the following questions:
Appendix 2
Keeping Information Secure
Passwords
•Use secure passwords, at least 8 characters long, combining upper case, lower case, numerals, and special characters
•Do not leave your password where others can see or access it
•Use different passwords for different accounts, systems or applications
At your desk
•Your offices may be open to visitors who should not have access to the information.
•Sensitive information should not be left where it can easily be seen or removed.
•Sensitive information should be locked away, or closed, when you are not using it.
•Don’t leave confidential information on copiers and printers.
•Waste paper containing personal or sensitive information should be shredded.
•Keep your workspace tidy – it is more obvious if something is missing.
At the end of the day:
•Tidy up and secure any sensitive information
•Lock drawers and filing cabinets
•Ensure that items such as laptops, mobile phones etc. are stored away securely
When out of the office (remote working):
•Be aware of the physical security risks and dangers of working within any remote/mobile environment.
•Do not leave equipment where it could attract the interests of an opportunist thief.
•In the home all information should be out of sight of visitors and secured when not in use.
•Laptop carry cases are easily identifiable by thieves so consider carrying them in something less obvious.
•Be aware that in public places (cafes, trains etc.) that there is a potential to be overlooked.
•Removable media devices (such as USB sticks) and paper documentation must not be stored with laptops.
•When travelling on public transport keep any equipment containing personal information in your sight at all times and check that you have left nothing behind when you leave.
Sharing data
•Do not share sensitive data internally or externally without permission from the CEO
•Abide by the rules and procedures of KCN’s Confidentiality and Data Protection Policy at all times
Electronic Communications
•Be aware of viruses and worms that are designed to infiltrate your computer.
•Do not open any email attachments unless you are confident of their source
•Report any suspicious items immediately
•Abide by the rules and procedures of KCN’s Electronic Communications Policy
Appendix 3
Data Breach Protocols under Confidentiality and Data Protection Policy
Data breaches can happen for a variety of reasons: human error; hardware or software malfunction; equipment failure; unauthorised access; hacking attacks.
Containment and recovery
Establish who needs to be made aware of the breach, how it should be contained.
Establish what can be done to recover the data e.g. from back-ups or other sources.
Determine if outside organisations need to be informed.
Assessing the level of risk
A low level risk would be e.g. a damaged laptop.
A high level risk would be theft or leakage of carer or staff records.
What type of data is involved and how sensitive is it?
What has happened to it?
How many individuals’ personal data is involved and who are they?
What harm may occur – reputation, financial?
What wider consequences may result e.g.in KCN’s reputation and stability?
Notification of a breach
Notification should have a clear purpose, whether to help protect individuals affected, or to allow regulatory organisations to perform their functions, provide advice and deal with complaints.
Not every breach will warrant notification, this must be weighed up in assessing the level of breach. If there is any doubt guidance could be sought from the police; ICO, and RBK.
If the breach involves a large number of people the ICO must be informed; Guidance on how to do this and the Form to be used is on their website. Advice should be sought on how to manage notification to those affected, and what steps they can take to protect themselves and mitigate any damage. A means of contact for ongoing information should be established.
Notification may need to be made to: insurance company; banks and credit card companies.
Evaluation and Response
It is important not simply to react to a specific breach; there may be systemic problems that could lead to another breach. It is vital to review and update policies and procedures, lines of responsibility, and staff/volunteer training and codes of practice.
Make sure what personal data is held , where and by whom, and what protection is in place i.e. passwords or encryption. Consider whether external consultants are needed to help.
Review data sharing procedures both within KCN and with other organisations.
Appendix 4
Privacy Statement
What we collect
We collect information about you when you register with us or request for information to be sent to you. We also collect information when you voluntarily complete surveys and provide feedback. We may collect the following information from you:
· Name and contact information including full address
· Demographic information such as age, ethnicity, gender, sexual orientation
· Other information relevant to the support and advice we provide to you including details of your caring role
What we do with the information we gather
We require this information to understand your needs and provide you with our services, and in particular for the following reasons:
· Internal record keeping and evaluation of our services
· We use the information to ensure that we can provide accurate and relevant advice.
· We use the information to update you with our activities, newsletters and other relevant information
Security
We are committed to ensuring that your information is secure. In order to prevent unauthorised access or disclosure, we have put in place suitable physical, electronic and managerial procedures to safeguard and secure the information we collect online.
How we use cookies
A cookie is a small file which asks permission to be placed on your computer's hard drive. Once you agree, the file is added and the cookie helps analyse web traffic or lets you know when you visit a particular site. Cookies allow web applications to respond to you as an individual. The web application can tailor its operations to your needs, likes and dislikes by gathering and remembering information about your preferences.
We use traffic log cookies to identify which pages are being used. This helps us analyse data about web page traffic and improve our website in order to tailor it to customer needs. We only use this information for statistical analysis purposes and then the data is removed from the system.
Overall, cookies help us provide you with a better website, by enabling us to monitor which pages you find useful and which you do not. A cookie in no way gives us access to your computer or any information about you, other than the data you choose to share with us.
You can choose to accept or decline cookies. Most web browsers automatically accept cookies, but you can usually modify your browser setting to decline cookies if you prefer. This may prevent you from taking full advantage of the website.
Links to other websites
Our website may contain links to other websites of interest. However, once you have used these links to leave our site, you should note that we do not have any control over that other website. Therefore, we cannot be responsible for the protection and privacy of any information which you provide whilst visiting such sites and such sites are not governed by this privacy statement. You should exercise caution and look at the privacy statement applicable to the website in question.
Controlling your personal information
You may choose to restrict the collection or use of your personal information in the following ways:
· We will not use your information for any other purposes other than providing information, advice and support to you
· If you have previously agreed to us using your personal information, you may change your mind at any time by writing to or emailing us at [info@kingstoncarers.org.uk]
We will not sell, distribute or lease your personal information to third parties. We may use your personal information to act on your behalf in dealing with other organisations such as the local authority. However, we will only pass on your personal information with your consent or where there is a legal or safeguarding need.
You may request details of personal information which we hold about you under the Data Protection Act 2018. A small fee may be payable. If you would like a copy of the information held on you please write to (Kingston Carers’ Network, 418 Ewell Road, Surbiton, KT6 7HF).
If you believe that any information we are holding on you is incorrect or incomplete, please write to or email us as soon as possible, at the above address. We will promptly correct any information found to be incorrect.